
The cyber world is ever growing and in this vast world, no business is 100% safe & insured against cyber attacks. With so many threats out there incurred every minute, it is hard to detect each one and prevent them all. In this world of disruptive technology if organisations want to remain competitive, keeping their IT infrastructure security up-to-date is a must.
The Government, cybersecurity experts & other groups are taking various initiatives to spread awareness on cyber attacks but despite these attempts, organisations fail to take their cybersecurity seriously, we may say this is due to lack of awareness, increase in expense or companies simply not wanting to take the pains to prevent breaches.
“When things are going well, it is hard to sell the message of security to stakeholders and get support from across the business. When things are not going so well (e.g. you’ve had a breach), it means high pressure and a lot of focus on your performance” says Alex Woerndle, Principal Analyst Cybersecurity, Ecosystm.
Cyber attacks happen without notice. While there are many cyber experts present to help and provide consultation to the organisations, knowing beforehand about the attacks and strengthening your cybersecurity will safeguard you against serious ramifications.
Let’s Understand – What is a Cyber Attack?
A cyber attack is a deliberate attempt by an individual or a community working together to tap into an existing or a newly discovered vulnerability in the system, network, firmware or software resulting in complete control or gaining information from the victim’s system. While measuring the ill-effects of a cyber attack, we can say that with access to critical data one can exploit sensitive information, identity and may cause serious damage to an organisation or personal identity. Sometimes, a cyber attack is also referred to as computer network exploitation (CNE) or a computer network attack (CNA).
The other common terms used in association with a cyber attack are threat, vulnerability, and risk. Often these terms are mingled together in our day-to-day usage, but they all mean something different. Let’s try to uncover the basic difference between a threat, a vulnerability, and a risk.
A threat can be explained as an activity to exploit a weakness in a system, to cause harm or reveal the underlying assets. It always involves a person responsible for performing threat actions to impact the system’s security known as a threat actor.
A vulnerability is an unknown system flaw or a known weakness that could potentially be exploited by a person also known as a hacker. In other words, it can be known or unknown issues within a system or its software that can be exploited by hackers.
Together, when a threat acts and exploits a vulnerability, this may result in the development of a situation known as a risk. A risk could lead to potential loss or damage to a business.
Understanding threats, vulnerabilities, risks and other components will help you to act against cyber attacks but this may raise another question on why someone would try to harm your business.
So Why do Cyber Attacks Happen?
The people behind a cyber attack could be hackers, a team or a dark web organisation who work with an ulterior motive to commit a digital crime or to gain access to one’s system through a cyber attack. Collectively we may refer to them as cyber criminals. Cyber criminals try to identify vulnerability to crackdown a system.Below are some of the common reasons why a cyber attack happens.
Financial Gain
This is one of the most well-known types of cyber crime. The motive of cyber criminals here is to get easy access to money and the ways they make this happen is through frauds, demands, data breaches or direct attacks. What attackers try to steal are the business’ financial details or sensitive data/intellectual property, customer financial data or databases, staff or client credentials. By gaining access to these, the attackers get in a position to easily access a secured system and exploit it for their financial gains.
Hacktivism – Political or Social
Hacktivism is an activity involving anonymous organisations breaking into an organisation’s IT infrastructure for political or social reasons. Hacktivists mount cyber attacks to access information that can damage the intended target or perform activities to hurt or lower the reputation of certain bodies. Government and political bodies are often the targets of hacktivism.
Intellectual Challenge
Cyber world experts are sometimes challenged by the thrill of hacking or may develop a personality living in a virtual world pushing them to hack into a network with an intention of identifying system vulnerabilities. Generally, hackers are referred to as people with bad motives but hackers are not necessarily criminals as some of them help organisations to test systems, recognise backdoors, loopholes or vulnerabilities in a system which is termed as ‘white hat’ hacking. Knowing the vulnerabilities in the existing IT infrastructure and services may protect organisations from some serious future consequences.
Espionage
Stealing classified information, sensitive data or intellectual property from a government entity or a competitive organisation is a common form of espionage attack. The examples of an espionage attack could be stealing trade and military secrets or technologies or potential system flaws which may pose an influential threat to a nation.
Organised Cyber Crime
Digital technology has empowered individuals with some serious fire-power. IMs and chat technology have made it easy for individuals to form teams or an organisation to commit crimes on the web. Sometimes several groups form communities to commit a serious cyber crime – planned, coordinated and conducted together at a macro level.
Disruption
Aiming to disrupt business, or the operations of critical infrastructure, can be undertaken just to demonstrate security weaknesses, the hacker’s general disapproval for the business, or even to cause extensive operational, financial and physical damage to their target.
The Vulnerabilities that a Business can Experience
Data breaches occur every minute and unknown threats and vulnerabilities always pose a risk for a business. To stay protected, it is always better to know and understand the types of threats or vulnerabilities that a business can experience rather than later raising questions on how the attackers got in.
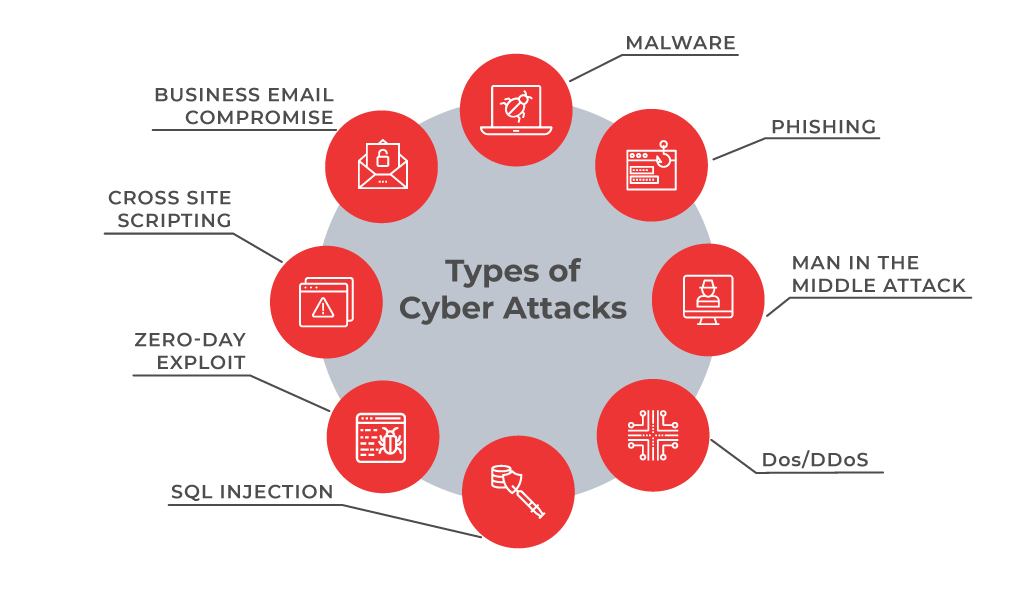
- Malware . A malware is a type of cyber attack where malicious software is installed on the victim’s systems through executable files usually without the user’s knowledge. Malware includes malicious software, including spyware, ransomware, viruses, and worms. After installation, a malware can keep track of the user’s activity or can trigger codes resulting into access to sensitive information, login details, credit cards or intellectual properties by the hacker.
- Phishing. Phishing refers to spoofing or deceptive communications activities performed by the attackers that appear to originate from a credible source such as emails, messages, legitimate websites that are disguised. Through phishing, attackers try to fetch sensitive information, user details, credit card numbers or make fraudulent attempts.
- Man-in-the-middle attack. These attacks happen with relaying or altering the communication channels. This can be communication between organisations and cloud server or over unsecured networks.
- DoS/DDoS. A DoS/DDoS attack aims at flooding the target website with overwhelming traffic to exhaust resources and bandwidth of the system. These are not to bring down a website but to breach a security perimeter and smoke out the online systems. This can reduce a user base or may bring down the entire network.
- SQL Injection. This is injecting a nefarious code or statements into SQL queries or a database server to extract information from the database or to take a data dump of the complete database.
- Zero-day exploit. Zero-day is a software security flaw which is known to the software developers. Attackers try to exploit a vulnerability before a patch or solution is implemented to capture the system with known weaknesses.
- Cross Site Scripting. XSS attacks occur when a web app sends malicious code in the form of a side script to another user thus bypassing access controls of the site to same as the origin.
- Business Email compromise. This is an attack to spoof business emails and gain illegal access to company accounts and ids to defraud the company or its employees.
According to Woerndle, “Nowadays, most of the reported attacks appear to be email-focused either with the intention to encrypt the infected systems to demand payment of a ransom for the keys (i.e. ransomware), to steal credentials (subsequently used for further attacks on other systems and applications) or to steal information that can be sold for profit on the black markets. “
Some of the World’s Largest Data Breaches
Cyber attacks have become a repeated theme every year and we hear quite often about the data breaches. Here’s a visualisation of some of the world’s largest data breaches that have occurred in the past few years.
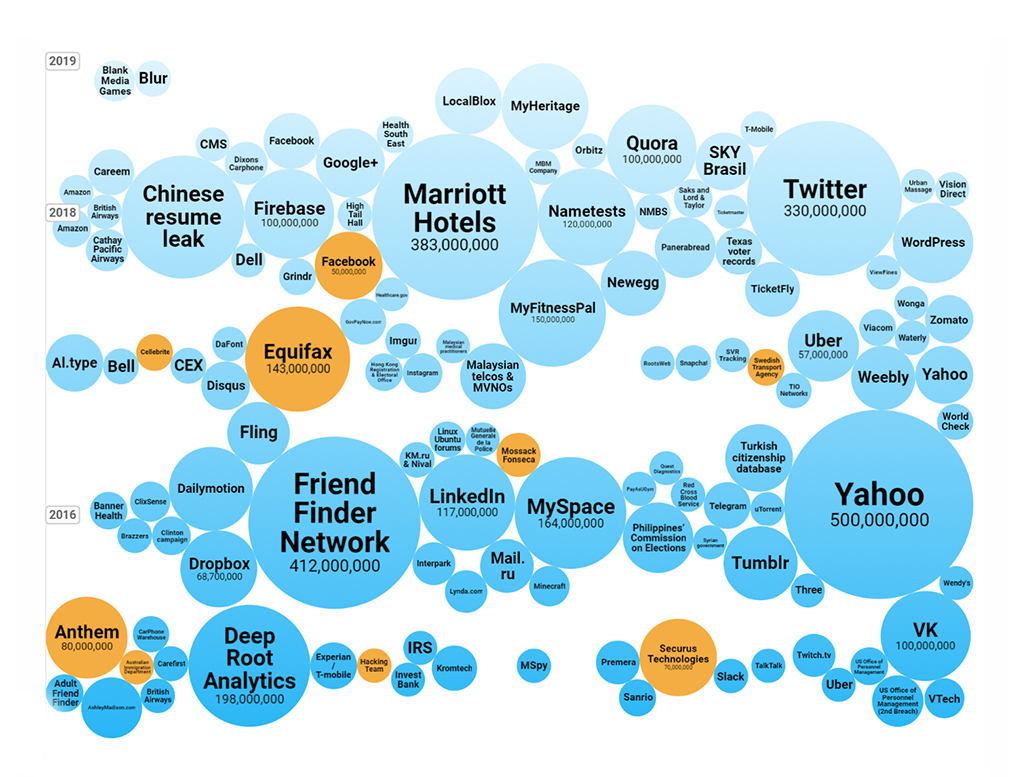
Source: Informationisbeautiful-worlds biggest data breaches hacks
How to Prevent Cyber Attacks?
To minimise cyber attacks, businesses can put some counter-measures in place. It is a smart move to be prepared for serious circumstances and act reactively with security measures.
Secure assets. It is always considered a security best practice to keep your systems and infrastructure updated with latest security patches and updates which are released from vendors or manufacturers on a regular basis.
Conduct threat assessment. Vulnerabilities can arise within your own system or potentially from other sources which are not directly under your control, but they can be identified if you are aware. Perform regular due diligence of your system or network security.
Stay informed on threats. News articles, software companies, cyber security organisations often release information on threats and vulnerabilities that can help you stay informed and act against threats.
Formulate steps to avoid threats. Training and regular information to organisations and employees can prevent many attacks from happening. If your users or employees are aware and informed they can escape the threats. Keep strong passwords, encrypt sensitive information, safeguard accounts, use firewalls to prevent attacks.
Plan an incident response. Create plans and approaches to react against a cyber attack to manage and limit the damage. Always keep your systems backed up online/offline and prepare your IT team to deal with it. You may also take advice or may hire experts to strengthen your infrastructure security.
It is rightly believed that prevention is better than cure. Speaking on the subject, Alex Woerndle, conveys that “the fundamentals are always the most critical starting points – focus on your system and application hardening and patching processes, deploy and actively maintain endpoint protections (e.g. anti-virus), restrict the permissions users have on their devices and invest in regular training and awareness for all staff. Beyond that, ensure all systems are backed up regularly, and deploy (and encourage all users to apply in their everyday lives) multi-factor authentication wherever possible.”
Considering the recent information security breaches, governments around the world are actively forming committees and taking measures to fight against cyber attacks. The governments of various nations have published some guidelines and measures to prevent cyber attacks.
The NIST Cybersecurity Framework, US, provides a policy framework of computer security guidance for organisations to assess and improve their ability to prevent, detect, and respond to cyber-attacks. The framework has been translated into many languages and is used by various governments and organisations across the world.
The Australian Government (via Australian Signals Directorate – part of Defence) has published some very good guidelines – called the ‘Essential 8’ and ‘Strategies to Mitigate Cyber Security Incidents’. The Essential 8 are a very user-friendly guide for businesses and provide protection against 80% of the most common cyber attacks
The UK Government has also come out with very useful information to help organisations.
Recently, Singapore opened a new cybersecurity school and the Ministry of Defence (MINDEF), is planning to hire security experts for their cyber defense strategy.
Cybersecurity is a challenging area and is a very broad discipline that requires skills across technology, forensics, business management, risk and compliance, education, communication, technical support, and others.
Negligence can impair reputation and lead to commercial losses but by understanding the security aspects, one can become aware of the potential threat and be in a better position to counteract it, or even preempt it.
This is just a glimpse to give you some insights into areas of cybersecurity and what goes under the surface. For specific details, you may get in touch with us or speak with a cybersecurity expert.







