There has been a widespread adoption of hybrid and multi-cloud architectures in the recent past and this trend is only expected to go up in the near future. A hybrid cloud adoption has its challenges though; including the need for organisations to baseline their security practices across so many different environments. Organisations that are aware of the cybersecurity risks associated are increasingly looking for external specialised help in managing their cloud security measures, especially with an aim to automate the processes.
Zscaler Acquires CloudNeeti
In a recent announcement, Zscaler announced its intentions to acquire Cloudneeti, a niche Cloud Security Posture Management (CSPM) start-up based in Redmond, Washington. This is set to expand Zscaler’s Cloud Security Platform capabilities to include data protection. With this acquisition, Zscaler will be able to complement its own offerings to provide:
- A complete Data Protection and Exposure Prevention suite, that works across locations, users and applications and ensures better compliance with regulations
- A Unified Compliance Assurance platform that provides compliance visibility and breach mitigation across the multiple SaaS applications an organisation uses
- Risk Reduction through automated remediations following both industry compliance laws and organisations’ own risk management program guidelines
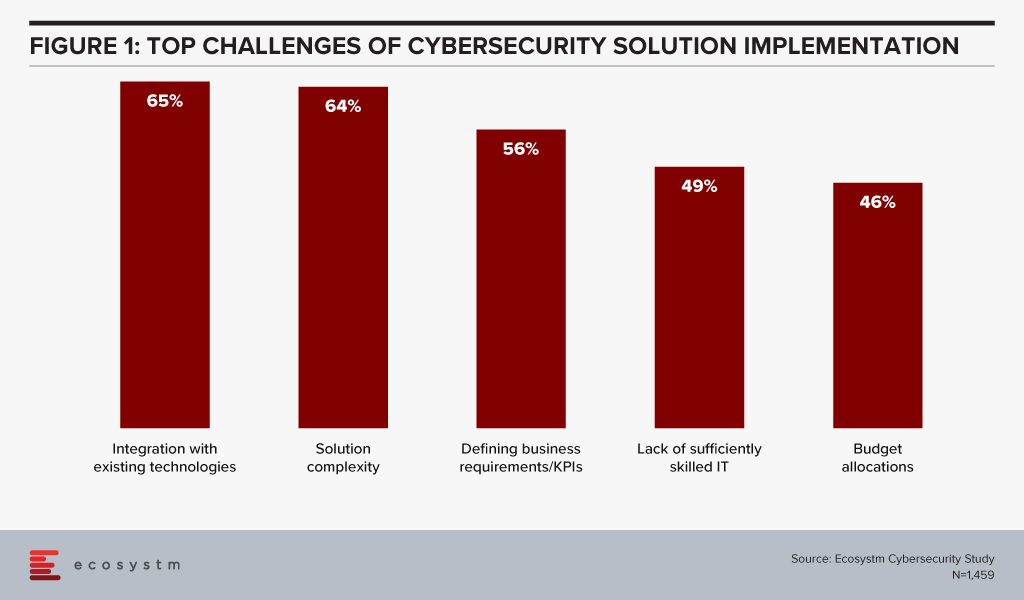
Ecosystm research finds that organisations are struggling with their cybersecurity implementations, especially as the solutions get increasingly complicated to combat the complex and evolving threat environment (Figure 1). Integration with existing cybersecurity measures, and a lack of sufficiently skilled IT staff to handle the myriad needs of the multiple systems and applications, builds a strong case for automation in cybersecurity practices.
Ecosystm Principal Advisor, Alex Woerndle says, “Automation is critical in cybersecurity, given the volume of data, alerts and incidents that are being dealt with on a daily basis, globally. Automating recurrent and high-volume tasks is a critical step in getting on top of this challenge.”
Importance of Automating Cybersecurity Processes
Woerndle sees a growing role for CSPM providers for multiple reasons. “Firstly, a lot of companies are finding that they cannot be ‘fully cloud’ and as such, end up with a complex architecture spanning on-premise, private cloud environments and multiple public cloud tenancies. Secondly, due to poorly planned cloud migrations, changing priorities, differences in service requirements, cost differences and also personal preferences across multiple teams, a lot of companies end up consuming different services across multiple public cloud providers (Azure, AWS, GCP, and so on). IT teams are struggling to be experts in all aspects of the shared responsibility model and with the capabilities to secure the various services. Finally, there is a constant stream of upgrades and addition of new services team members, given the easy accessibility public cloud environments provide. CSPM solutions provide the ability to establish baselines, enforce security controls and run regular checks to ensure compliance. Doing this manually is time consuming, expensive and always three steps behind.”
Woerndle also sees further complications because of the COVID-19 crisis. “COVID-19 has shifted the world to remote working overnight. Once workers are outside of the trusted corporate network and have access to cloud resources from their home networks, additional complexity to the corporate security posture is highlighted. Depending on how organisations have prepared for this, they either maintain control of all services and applications, and the access into each, or if not prepared, open direct access to a lot of unsecured applications from potentially very unsecured networks.” In fact Zscaler has seen its stock prices rising in the aftermath of the global crisis.
However, Woerndle warns, “While the conversation certainly supports the use of CSPMs, there is a lot more to it in terms of securing home networks, identity and access management, and so on.”
Zscaler’s acquisition of CloudNeeti certainly appears to be a timely move, in the current environment when organisations are struggling with a lack of resources with the extensive knowledge to understand all private and public cloud environments. There are controls required to secure each application, resource and system within an organisation – along with the time and effort required to implement, monitor, audit and improve cybersecurity measures over time.