The global cloud market is dominated by AWS, Microsoft, IBM, Google, and Alibaba, all of whom are strengthening their grip on the global market. Their continued dominance means that over time, organisations reliance on them will rise.
In order to reduce the dependency on American and Chinese cloud providers, and to counteract mounting data security and privacy concerns, France and Germany are drawing plans to strengthen Europe’s data infrastructure.
The countries announced a proposal to boost Europe’s cloud computing sector in the form of a homegrown, and government-backed, data infrastructure project to establish a safe and sovereign European data infrastructure.
Last month, France recruited tech companies Dassault Systemes – a French software company and OVH – a privately held French cloud computing company to provide plans to break the dominance of U.S. cloud companies.
To serve as an alternative to American and Chinese cloud providers and enable innovative business models, Germany and France have collaborated on developing the core concepts of the European cloud network, called Gaia-X, before trying to get other European countries to join early next year. As a part of Gaia-X, the cloud participants will be required to certify their customers’ information security – e.g. where it is stored and how it is processed. Germany has formed a broad alliance of associations and companies, including Siemens, SAP, Deutsche Bank and Deutsche Telekom for the European cloud project. Claus Mortensen, Principal Advisor at Ecosystm said, “the project is focusing on security at its core and the idea of certifying customers could further help ensure data security and data privacy.”
Mortensen continued, “so far, cloud uptake in Europe has trailed other regions – especially North America and a number of countries in Asia. Whether or not these projects will succeed depends on several factors: the political will behind the project, whether the process becomes overly complicated and lengthy and whether the different companies involved can cooperate when needed.”
Mortensen added, “there is nothing wrong with countries in the EU building cloud infrastructure and issuing tenders for private companies to build this infrastructure – as long as the tenders have followed EU rules and they provide non-discriminatory access to this infrastructure. In the end, it will come down to how the infrastructure is managed and who owns it.”
French and German government officials are set to meet this month, where other interested companies will be invited to provide their inputs. The aim is to create a governance structure for the initiative before the end of the year.
Another goal of pushing homegrown cloud platforms is to support European companies in their development of AI and algorithms and to help them protect against the marketplace which is becoming the domain of a few big vendors.
“The existing cloud giants have technical know-how and readiness, so competing with them will not be easy unless the project can differentiate in ways other than the typical selling points such as price, scalability, granularity, etc. The political backers of this project may be relying on the ‘Made in Europe’ case, but I doubt that will be enough to persuade the bulk of future potential customers” said Mortensen. “More choice is always good for customers and if an objective of this project is to increase cloud uptake in Europe, this would certainly help.”
According to a recently-released report, e-Conomy Southeast Asia 2019 by Google, Temasek Holdings Pte and Bain & Co., Southeast Asia’s Internet economy could exceed US$100 billion this year (a 39% increase from 2018) and will touch US$300 billion by 2025. The report states that Southeast Asian’s are ‘the most engaged mobile Internet users in the world’, and the region is becoming one of the world’s fastest-growing areas for Internet users – fueled by 360 million existing online users.
Analysing the current and future potential of the Southeast Asian Internet economy across its six largest markets – Indonesia, Malaysia, the Philippines, Singapore, Thailand, and Vietnam – it has been a momentous time for online travel services, online media, ride-hailing services, eCommerce, and digital financial services to leverage digital tools.
Southeast Asia’s Internet Economy is expected to grow
Southeast Asia’s fundamental changes in consumer behaviour and engagement with mobile internet have grown demand for eCommerce and Ride-Hailing services.
eCommerce is the largest and fastest-growing sector with more than 150 million Southeast Asians engaged in online shopping, and this is indicative of the fundamental changes in the way people consume eCommerce services.
Growth of digital financial services
Currently, Southeast Asia lacks adequate financial services as out of nearly 400 million adults in the region an estimated 98 million are underbanked and 198 million are unbanked.
Commenting on the expanding Internet economy, Ecosystm Principal Advisor – Growth & Expansion, Paul Gestro said “Vietnam, Philippines, and Indonesia will be the markets that could benefit the most from the US$100 billion Internet economy. This is primarily because a large percentage of the population in these markets is unbanked. With the growth and access to some form of banking (traditional or virtual) and the ability to transact a payment, this will have a huge influence on Fintech solutions.”
Another key trend is the growth of digital payment and financial services in the region. The growth of digital financial services will make the Internet economy more wide-ranging and consumers will enjoy greater access to Digital Payments and eCommerce.
Gestro added, “Insurance, payments and investment services will add to what we do now with ride-sharing and food delivery services. We will instantly make decisions on insurance and investment products and deals backed up by seamless payment mechanisms and different forms of payment.”
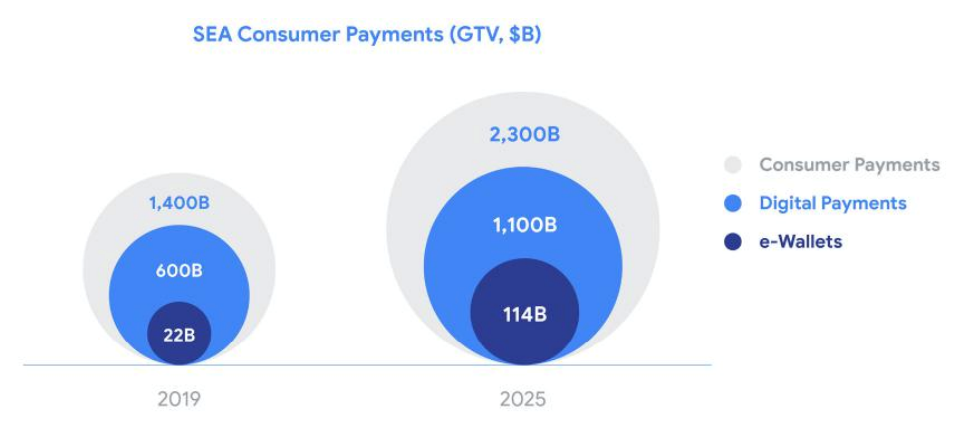
While most Digital Financial Services are still nascent, Digital Payments are expected to cross US$1 trillion by 2025 and this could open investment opportunities.
“The open investment opportunities for investors in Southeast Asia’s internet economy will be investing in applications that are mobile-ready. There will be a growth in mobile transactions and services, and companies that take a mobile-first approach will be the investors’ target,” said Gestro.
The report advises governments of Southeast Asian countries to align digital financial service regulations across the region to facilitate the development of regional business models and help channel resources towards investments in world-class tech and talent.
Despite the growing Internet economy, talent constraints remain a pressing concern as the Internet economy expands. Gestro said, “programmes in schools are required to promote a digital understanding and offer clear pathways to build knowledge and skills required for an Internet economy. This also includes companies who should be offering internships and working closely with universities to make sure the courses match where talent is needed.”
The use of mobile phones and mobile applications will connect consumers to a raft of services they previously lacked, and allow business owners and leaders to reach a whole new population of customers that was previously under-served. There’s still a lot of work to be done to ensure Southeast Asia’s Internet economy reaches its potential.
A group of some of the world’s largest technology companies including Alibaba, ARM, Baidu, Google Cloud, IBM, Intel, Red Hat, Swisscom, and Tencent have come together to form “Confidential Computing Consortium”, an association established by the Linux Foundation to improve the security of data while in use, and hosted by them at ConfidentialComputing.io.
Confidential Computing Consortium aims to define and accelerate the adoption of Confidential Computing by bringing together a community of open-source technologies and experts.
New Cross-Industry Effort
There are many government agencies, consortiums, and software and hardware vendors working on data security so a key question here is “who needs it?”
Commenting on CCC, Claus Mortensen, Principal Advisor at Ecosystm said, “whether this is really ‘needed’ is a matter of perspective though. Many would argue, that a project driven by technology giants is contrary to the grassroots approach of earlier open source projects. However, Confidential Computing is a complex area that involves both hardware and software. Also, the stakes have become high for businesses and consumers alike, as data privacy has become the focal point. Arguably, the big tech companies need this Open Source initiative more than anyone at the moment.”
How CCC would benefit enterprises and business users?
With the increasing adoption of the cloud environments, on-premise servers, the edge, IoT and other technologies, it’s crucial for enterprises to increase the security of the data. While there have been approaches to encrypt data at rest (storage) and in transit (network) it’s quite challenging to fully encrypt the data life cycle and that’s what Confidential Computing aims to solve.
Mortensen said, “when it comes to data security, the actual computing part of the data life-cycle is arguably the weakest link and with the recent increased focus on privacy among the public, this ‘weakness’ could possibly be a stumbling block in the further development and update of cloud computing.” Mortensen added, “that doing it as part of an open-source initiative makes sense, not only because the open-source approach is a good development and collaboration environment – but, crucially, it also gives the initiative an air of openness and trustworthiness.”
To drive the initiative, members have planned to make a series of open source project contributions to the Confidential Computing Consortium.
- Intel will contribute Software Guard Extensions (SGX) SDK to the project. This is hardware-based memory level data protection, where data and operations are encrypted in the memory and isolated from the rest of the system resources and software components.
- Microsoft will be sharing the Open Enclave SDK to develop broader industry collaboration and ensure a truly open development approach. The open-source framework allows developers to build a Trusted Execution Environment (TEE) applications.
- Red Hat will provide its Enarx to the consortium. – an open-source project aimed at reducing the number of layers (application, kernel, container engine, bootloader) in a running workload environment.
Mortensen said, “like other open-source initiatives, this would allow businesses to contribute and further develop Confidential Computing. This, in turn, can ensure further uptake and the development of new use cases for the technology.”
How Data Security Efforts will shape up
Confidential Computing is a part of a bigger approach to privacy and data and we may see other possible developments around AI, in distributed computing, and with Big Data analysis.
“Initiatives that can be seen as part of the same bucket include Google’s “Federated Learning” where AI learning on data is distributed privately. This allows Google to apply AI to data on the users’ devices without Google actually seeing the data. The data remains on the user’s device and all that is sent back to Google is the input or learning that the data has provided” said Mortensen.
Consequently, Confidential Computing seems to ease matters for data security at this point and the collaboration expects the results will lead to greater control and transparency of data for users.
Let us know your opinion on the Confidential Computing Consortium in the comments.
Apple and Intel have signed an agreement where Apple will acquire Intel’s smartphone modem business for a deal valued at $1 billion. Apple will gain Intel’s Intellectual Property, equipment, leases, and approximately 2200 Intel employees will join Apple.
The deal is Apple’s second-largest ever after its $3.2bn purchase of Beats Electronics in 2014. The deal is expected to close at the end of the year and Intel will continue to develop modems for non-smartphone applications such as industrial equipment, autonomous vehicles and personal computers.
What Apple has really acquired from Intel?
Beyond getting 2,200 employees from Intel’s modem group along with the accompanying 17,000 patents, Apple now has the intellectual property to develop a modem that can be integrated with Apple (system-on-a-chip) or SOC.
Commenting on Apple’s acquisition of Intel modem business, Ecosystm Executive Analyst, Vernon Turner said “given its performance-driven and highly vertically integrated product line, Apple had its own ambitions to build its own modem. However, despite being capable of building chips, Apple lacked the knowledge to build a modem. To solve that issue, it would always have had to license patents from a 3rd party, unless they buy the company that has the patents instead.”
Aligning with the fifth generation
The acquisition of Intel modem business displays Apple’s ambition to ramp up on 5G technology. The foothold in the 5G modem business is also expected to reduce Apple’s reliance on Qualcomm, its modem supplier. Speaking of the competition, Apple’s global rivals in the handset business – Samsung Electronics and Huawei – already produce their own modem chips.
“Apple has a lot of catching up to Samsung and Huawei in the 5G modem market, and while it has now gained technology from Intel, there is still a significant gap and it will be a haul for Apple to suddenly catch up and overtake them,” said Turner. “Apple’s modem supplier, Qualcomm isn’t likely to be worried by this news either – it too has a lead of several years. The bottom line is that Apple didn’t have a lot of options to turn too if it wanted to be in control of as much of the phone IP stack as possible. It purchased a modem supplier that was perhaps the weakest in the market and had already thrown in the towel on their mobile modem business.”
Apple will take some time to absorb the Intel team into its business and likewise with the modem roadmap. The deal is a step in Apple’s journey to make all of its own smartphone chips and having a more self-sufficient supply chain.
At the 7th Personal Data Protection Seminar, Minister for Communications and Information S. Iswaran announced a framework to bolster Singapore’s digital economy and to drive Singapore’s vision of turning the country into a regional data protection hub.
The Personal Data Protection Commission (PDPC), which oversees the country’s Personal Data Protection Act (PDPA), has developed a new framework to better support organisations in the hiring and training requirements of Data Protection Officers.
Why the Need?
PDPA has been around for a while and the new framework is brought into practice to enable a greater focus of government and organisations on data privacy. According to Ecosystm’s expert on GDPR and Data Privacy, Claus Mortensen, “the initiative reflects the difference between ‘theory’ and ‘practice’ when it comes to data security. PDPA is not making changes to the present regulatory framework, but they are putting together a program and guidelines for how companies can apply and abide by the present regulatory framework.”
Ensuring PDPA framework compliance
The PDPC plans to collaborate with the National Trades Union Congress (NTUC), Employment and Employability Institute (e2i) and NTUC LearningHub to create a year-long pilot training program to train at least 500 data protection officers in its first intake. The Data Protection Officers would help to manage the complex and highly sensitive task of data flows.
To ensure the data flow mechanisms and to ensure security, Infocomm Media Development Authority (IMDA) has been appointed as Singapore’s Accountability Agent (AA) for the Asia-Pacific Economic Cooperation (APEC) Cross Border Privacy Rules (CBPR) and Privacy Recognition for Processors (PRP) Systems certifications. IMDA will allow Singaporean organisations to be certified in APEC CBPR and PRP Systems for accountable data transfers.
“The PDPA requires a data protection officer to be appointed in every organisation. This framework is focused on educating and certifying these officers. However, it mostly makes it easier for slightly larger companies who can afford to send employees on longer training programs or who are able to hire people, who have taken the certificates. Smaller organisations – such as start-ups – would benefit more from detailed guidelines and from on-premises guidance. Establishing a framework for such services could be the next area of focus for the PDPC.” said Mortensen.
Legislature for the data handling and exchange practices
The private data has become an increased target of hackers as well as an international commodity. Attackers always mine the cyberspace for any leaks or financial information that they can exploit to their advantage.
“Managing sensitive data is notoriously complicated – especially for ‘legacy’ companies that still have or rely on non-digitised data. Even when all data is digital, employees may have copies on their PCs, they may have partial backups on removable media, some data may need to be shared with sub-contractors, moved around between cloud providers, etc. This can make it very difficult to map out PDPA relevant data in the organisation. Even when the data has been mapped, it can be difficult to ensure that all business and data processes are compliant. This is where on-premises guidance can make a difference,” said Mortensen. “While the government clearly aim the new framework initiatives at helping SMEs, it will help further protect consumer’s sensitive data.”
Importance of Cyber Security
A business harnessing digital technology can’t afford to gamble with sensitive data and rising cyber-attacks. The government is taking initiatives by forming guidelines and regulations to prevent cyber-attacks, but it is the responsibility of businesses to have a cybersecurity strategy in place to prevent a breach. If a business becomes a victim of hacking, it is perceived as a failure to the company.
The government passed the PDPA law and compliance to ensure that businesses understand the importance of cybersecurity. Therefore, every business, organisation or academic institution must ensure compliance with the data protection act and must have security best practices to safeguard the data of its customers.
8×8 an enterprise communications player in the areas of voice, video, chat and contact centre solutions announced the acquisition Wavecell, a Singapore-based global Communications Platform-as-a-Service (CPaaS) provider last week. The deal is estimated to be for about USD 125 million in cash and stocks.
With this acquisition, 8×8 can leverage their CPaaS platform capabilities to enable companies to develop and embed communications features more easily. Enterprises can get direct access to pre-built features via Application Programming Interfaces (APIs) leveraging CPaaS. These APIs let developers pay for the services they need when building voice, video, chat, SMS, and web capabilities. By using a cloud CPaaS, developers can also eliminate lengthy development times and reduce time to market.
What does this acquisition mean for 8×8 in the Asia Pacific region?
- Establishes their presence in the rapidly growing CPaaS space. The CPaaS market is growing rapidly which includes key players like Twillio and Vonage. The Wavecell acquisition will allow 8×8 to offer a platform for providing SMS, messaging, voice, and video APIs globally to both enterprises and developers. Wavecell offers a complete CPaaS solution including a cloud API platform with SMS, chat apps, video interaction and voice APIs that enable mission-critical enterprise applications such as Application-to-Person (A2P) messaging, omnichannel customer journeys and multi-factor authentication at scale.
- Expands their footprint in the Asia Pacific region. With this acquisition, 8×8 will now have a good footprint in markets which includes Singapore, Indonesia, Philippines, Thailand, and Hong Kong. 8×8 is active mainly in the ANZ region. Wavecell has more than 500 enterprise including names such as Paidy, Tokopedia and Lalamove. Wavecell also brings an R&D centre in Asia which allows 8×8 to further accelerate growth in product innovation and delivery.
- Gives access to a large enterprise developer community. Wavecell have built a robust enterprise developer community over the past several years which has leveraged their API platform and software development kits. 8×8 can now enable application providers, enterprise developers, and customers to access and natively integrate their enterprise applications with 8×8’s voice, video and messaging services.
- Provides global coverage for multi-channel communications. Wavecell has established relationships with 192 network operators worldwide and business partners such as WhatsApp. Its carrier-grade infrastructure enables customers to share more than two billion messages per year across these channels. This global network enables Wavecell customers such as Lalamove, to use SMS to immediately notify customers of their ordering and delivery requests. The acquisition extends 8×8’s global carrier relationships and network support to hundreds of additional carriers, enabling 8×8 to further optimise their global service delivery for enterprise customers anywhere they operate around the world.
Ecosystm Comments
The CPaaS market is growing rapidly globally. Developers want to easily add real-time communication capabilities such as voice, video and chat apps through APIs with a faster time to market. The ability to do it easily and to be able to scale without a lengthy implementation cycle and at an affordable cost is becoming key. This acquisition will help 8×8 compete in the growing CPaaS market where players such as Twillio and Vonage are growing their presence rapidly.
The enterprise communications and contact centre segments are highly competitive spaces in Asia Pacific with several new entrants in the region in the last 18 months. These players, mainly from North America, offer strong capabilities in the areas of voice, video, collaboration and contact centres. 8×8 has been strong predominantly in the ANZ region. They have plans to open an office in Japan later this year. The Wavecell acquisition will help 8×8 expand and open doors for their core product offerings in South East Asia and Hong Kong. Wavecell’s large customer base of over 500 customers will give 8×8 an opportunity to upsell their enterprise and contact centre applications.
Some customers are still buying enterprise and contact centre technology from various vendors depending on who is the right vendor for voice, video, contact centre and other applications as opposed to working with one vendor for their end-to-end solution. 8×8’s advantage against some of their competitors is that they own the entire stack of their offerings. That has been important to some of their customers who have said that it has also benefited them from a security perspective. Most of their clients who have moved to their platform have done so due to scalablity, ease of implementation and fast deployment times.
This acquisition is definitely a step in the right direction for 8×8.