2023 has been an eventful year. In May, the WHO announced that the pandemic was no longer a global public health emergency. However, other influencers in 2023 will continue to impact the market, well into 2024 and beyond.
Global Conflicts. The Russian invasion of Ukraine persisted; the Israeli-Palestinian conflict escalated into war; African nations continued to see armed conflicts and political crises; there has been significant population displacement.
Banking Crisis. American regional banks collapsed – Silicon Valley Bank and First Republic Bank collapses ranking as the third and second-largest banking collapses in US history; Credit Suisse was acquired by UBS in Switzerland.
Climate Emergency. The UN’s synthesis report found that there’s still a chance to limit global temperature increases by 1.5°C; Loss and Damage conversations continued without a significant impact.
Power of AI. The interest in generative AI models heated up; tech vendors incorporated foundational models in their enterprise offerings – Microsoft Copilot was launched; awareness of AI risks strengthened calls for Ethical/Responsible AI.
Click below to find out what Ecosystm analysts Achim Granzen, Darian Bird, Peter Carr, Sash Mukherjee and Tim Sheedy consider the top 5 tech market forces that will impact organisations in 2024.
Click here to download ‘Ecosystm Predicts: Tech Market Dynamics 2024’ as a PDF
#1 State-sponsored Attacks Will Alter the Nature Of Security Threats
It is becoming clearer that the post-Cold-War era is over, and we are transitioning to a multi-polar world. In this new age, malevolent governments will become increasingly emboldened to carry out cyber and physical attacks without the concern of sanction.
Unlike most malicious actors driven by profit today, state adversaries will be motivated to maximise disruption.
Rather than encrypting valuable data with ransomware, wiper malware will be deployed. State-sponsored attacks against critical infrastructure, such as transportation, energy, and undersea cables will be designed to inflict irreversible damage. The recent 23andme breach is an example of how ethnically directed attacks could be designed to sow fear and distrust. Additionally, even the threat of spyware and phishing will cause some activists, journalists, and politicians to self-censor.
#2 AI Legislation Breaches Will Occur, But Will Go Unpunished
With US President Biden’s recently published “Executive order on Safe, Secure and Trustworthy AI” and the European Union’s “AI Act” set for adoption by the European Parliament in mid-2024, codified and enforceable AI legislation is on the verge of becoming reality. However, oversight structures with powers to enforce the rules are currently not in place for either initiative and will take time to build out.
In 2024, the first instances of AI legislation violations will surface – potentially revealed by whistleblowers or significant public AI failures – but no legal action will be taken yet.
#3 AI Will Increase Net-New Carbon Emissions
In an age focused on reducing carbon and greenhouse gas emissions, AI is contributing to the opposite. Organisations often fail to track these emissions under the broader “Scope 3” category. Researchers at the University of Massachusetts, Amherst, found that training a single AI model can emit over 283T of carbon dioxide, equal to emissions from 62.6 gasoline-powered vehicles in a year.
Organisations rely on cloud providers for carbon emission reduction (Amazon targets net-zero by 2040, and Microsoft and Google aim for 2030, with the trajectory influencing global climate change); yet transparency on AI greenhouse gas emissions is limited. Diverse routes to net-zero will determine the level of greenhouse gas emissions.
Some argue that AI can help in better mapping a path to net-zero, but there is concern about whether the damage caused in the process will outweigh the benefits.
#4 ESG Will Transform into GSE to Become the Future of GRC
Previously viewed as a standalone concept, ESG will be increasingly recognised as integral to Governance, Risk, and Compliance (GRC) practices. The ‘E’ in ESG, representing environmental concerns, is becoming synonymous with compliance due to growing environmental regulations. The ‘S’, or social aspect, is merging with risk management, addressing contemporary issues such as ethical supply chains, workplace equity, and modern slavery, which traditional GRC models often overlook. Governance continues to be a crucial component.
The key to organisational adoption and transformation will be understanding that ESG is not an isolated function but is intricately linked with existing GRC capabilities.
This will present opportunities for GRC and Risk Management providers to adapt their current solutions, already deployed within organisations, to enhance ESG effectiveness. This strategy promises mutual benefits, improving compliance and risk management while simultaneously advancing ESG initiatives.
#5 Productivity Will Dominate Workforce Conversations
The skills discussions have shifted significantly over 2023. At the start of the year, HR leaders were still dealing with the ‘productivity conundrum’ – balancing employee flexibility and productivity in a hybrid work setting. There were also concerns about skills shortage, particularly in IT, as organisations prioritised tech-driven transformation and innovation.
Now, the focus is on assessing the pros and cons (mainly ROI) of providing employees with advanced productivity tools. For example, early studies on Microsoft Copilot showed that 70% of users experienced increased productivity. Discussions, including Narayana Murthy’s remarks on 70-hour work weeks, have re-ignited conversations about employee well-being and the impact of technology in enabling employees to achieve more in less time.
Against the backdrop of skills shortages and the need for better employee experience to retain talent, organisations are increasingly adopting/upgrading their productivity tools – starting with their Sales & Marketing functions.
The challenge of AI is that it is hard to build a business case when the outcomes are inherently uncertain. Unlike a traditional process improvement procedure, there are few guarantees that AI will solve the problem it is meant to solve. Organisations that have been experimenting with AI for some time are aware of this, and have begun to formalise their Proof of Concept (PoC) process to make it easily repeatable by anyone in the organisation who has a use case for AI. PoCs can validate assumptions, demonstrate the feasibility of an idea, and rally stakeholders behind the project.
PoCs are particularly useful at a time when AI is experiencing both heightened visibility and increased scrutiny. Boards, senior management, risk, legal and cybersecurity professionals are all scrutinising AI initiatives more closely to ensure they do not put the organisation at risk of breaking laws and regulations or damaging customer or supplier relationships.
13 Steps to Building an AI PoC
Despite seeming to be lightweight and easy to implement, a good PoC is actually methodologically sound and consistent in its approach. To implement a PoC for AI initiatives, organisations need to:
- Clearly define the problem. Businesses need to understand and clearly articulate the problem they want AI to solve. Is it about improving customer service, automating manual processes, enhancing product recommendations, or predicting machinery failure?
- Set clear objectives. What will success look like for the PoC? Is it about demonstrating technical feasibility, showing business value, or both? Set tangible metrics to evaluate the success of the PoC.
- Limit the scope. PoCs should be time-bound and narrow in scope. Instead of trying to tackle a broad problem, focus on a specific use case or a subset of data.
- Choose the right data. AI is heavily dependent on data. For a PoC, select a representative dataset that’s large enough to provide meaningful results but manageable within the constraints of the PoC.
- Build a multidisciplinary team. Involve team members from IT, data science, business units, and other relevant stakeholders. Their combined perspectives will ensure both technical and business feasibility.
- Prioritise speed over perfection. Use available tools and platforms to expedite the development process. It’s more important to quickly test assumptions than to build a highly polished solution.
- Document assumptions and limitations. Clearly state any assumptions made during the PoC, as well as known limitations. This helps set expectations and can guide future work.
- Present results clearly. Once the PoC is complete, create a clear and concise report or presentation that showcases the results, methodologies, and potential implications for the business.
- Get feedback. Allow stakeholders to provide feedback on the PoC. This includes end-users, technical teams, and business leaders. Their insights will help refine the approach and guide future iterations.
- Plan for the next steps. What actions need to follow a successful PoC demonstration? This might involve a pilot project with a larger scope, integrating the AI solution into existing systems, or scaling the solution across the organisation.
- Assess costs and ROI. Evaluate the costs associated with scaling the solution and compare it with the anticipated ROI. This will be crucial for securing budget and support for further expansion.
- Continually learn and iterate. AI is an evolving field. Use the PoC as a learning experience and be prepared to continually iterate on your solutions as technologies and business needs evolve.
- Consider ethical and social implications. Ensure that the AI initiative respects privacy, reduces bias, and upholds the ethical standards of the organisation. This is critical for building trust and ensuring long-term success.
Customising AI for Your Business
The primary purpose of a PoC is to validate an idea quickly and with minimal risk. It should provide a clear path for decision-makers to either proceed with a more comprehensive implementation or to pivot and explore alternative solutions. It is important for the legal, risk and cybersecurity teams to be aware of the outcomes and support further implementation.
AI initiatives will inevitably drive significant productivity and customer experience improvements – but not every solution will be right for the business. At Ecosystm, we have come across organisations that have employed conversational AI in their contact centres to achieve entirely distinct results – so the AI experience of peers and competitors may not be relevant. A consistent PoC process that trains business and technology teams across the organisation and encourages experimentation at every possible opportunity, would be far more useful.

There is no doubt that 2023 is off to an uncertain start. However, despite the economic headwinds we expect that some areas of technology will see continued growth. In fact, from our conversations with business and technology leaders, it appears that many organisations will take the opportunity to right-size their businesses, remove excess fat and waste, and accelerate their transformation efforts. The plan is to emerge from a global slowdown – leaner, smarter and better.
Where there is an opportunity to automate organisations will take it – and technology spend will trump people spend in 2023.
But it won’t all be smooth sailing as technology buyers become more discerning than ever and manage costs closely.
Here is what tech providers should focus on to remain resilient in these uncertain times.
- Be prepared to work harder – especially cloud and SaaS providers
- Help customers optimise costs
- Accelerate innovation to stay ahead of M&A activity
- Employ security to manage risk
- Prepare for product-led growth
Read on to find out why.
Download Be Alert – Not Alarmed: Analyst Guidance for Tech Providers as a PDF

Ransomware attacks have become a real threat to organisations world-wide – SonicWall reports that there were 304.7 million attacks globally in the first half of 2021, surpassing the full-year total for 2020. Organisations today are challenged with having the right cybersecurity measure in place, with cyber-attacks considered an inevitability.
This also challenges tech providers and cybersecurity vendors, as they have to constantly evolve their security offerings to protect their client organisations.
Ecosystm analysts, Alan Hesketh, Andrew Milroy and Claus Mortensen discuss the challenges tech providers face and how they are evolving their capabilities – organically, through acquisitions (Microsoft) and through partnerships (Google).

In this Insight, our guest author Anupam Verma talks about how the Global Capability Centres (GCCs) in India are poised to become Global Transformation Centres. “In the post-COVID world, industry boundaries are blurring, and business models are being transformed for the digital age. While traditional functions of GCCs will continue to be providing efficiencies, GCCs will be ‘Digital Transformation Centres’ for global businesses.”
India has a lot to offer to the world of technology and transformation. Attracted by the talent pool, enabling policies, digital infrastructure, and competitive cost structure, MNCs have long embraced India as a preferred destination for Global Capability Centres (GCCs). It has been reported that India has more than 1,700 GCCs with an estimated global market share of over 50%.
GCCs employ around 1 million Indian professionals and has an immense impact on the economy, contributing an estimated USD 30 billion. US MNCs have the largest presence in the market and the dominating industries are BSFI, Engineering & Manufacturing, Tech & Consulting.
GCC capabilities have always been evolving
The journey began with MNCs setting up captives for cost optimisation & operational excellence. GCCs started handling operations (such as back-office and business support functions), IT support (such as app development and maintenance, remote IT infrastructure, and help desk) and customer service contact centres for the parent organisation.
In the second phase, MNCs started leveraging GCCs as centers of excellence (CoE). The focus then was product innovation, Engineering Design & R&D. BFSI and Professional Services firms started expanding the scope to cover research, underwriting, and consulting etc. Some global MNCs that have large GCCs in India are Apple, Microsoft, Google, Nissan, Ford, Qualcomm, Cisco, Wells Fargo, Bank of America, Barclays, Standard Chartered, and KPMG.
In the post-COVID world, industry boundaries are blurring, and business models are being transformed for the digital age. While traditional functions of GCCs will continue to be providing efficiencies, GCCs will be “Digital Transformation Centres” for global businesses.
The New Age GCC in the post-COVID world
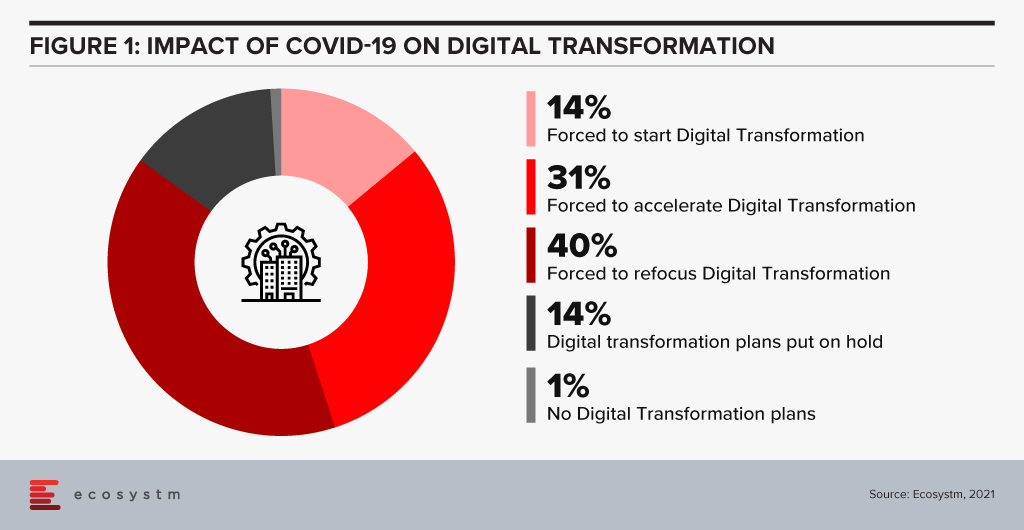
On one hand, the pandemic broke through cultural barriers that had prevented remote operations and work. The world became remote everything! On the other hand, it accelerated digital adoption in organisations. Businesses are re-imagining customer experiences and fast-tracking digital transformation enabled by technology (Figure 1). High digital adoption and rising customer expectations will also be a big catalyst for change.
In last few years, India has seen a surge in talent pool in emerging technologies such as data analytics, experience design, AI/ML, robotic process automation, IoT, cloud, blockchain and cybersecurity. GCCs in India will leverage this talent pool and play a pivotal role in enabling digital transformation at a global scale. GCCs will have direct and significant impacts on global business performance and top line growth creating long-term stakeholder value – and not be only about cost optimisation.
GCCs in India will also play an important role in digitisation and automation of existing processes, risk management and fraud prevention using data analytics and managing new risks like cybersecurity.
More and more MNCs in traditional businesses will add GCCs in India over the next decade and the existing 1,700 plus GCCs will grow in scale and scope focussing on innovation. Shift of supply chains to India will also be supported by Engineering R & D Centres. GCCs passed the pandemic test with flying colours when an exceptionally large workforce transitioned to the Work from Home model. In a matter of weeks, the resilience, continuity, and efficiency of GCCs returned to pre-pandemic levels with a distributed and remote workforce.
A Final Take
Having said that, I believe the growth spurt in GCCs in India will come from new-age businesses. Consumer-facing platforms (eCommerce marketplaces, Healthtechs, Edtechs, and Fintechs) are creating digital native businesses. As of June 2021, there are more than 700 unicorns trying to solve different problems using technology and data. Currently, very few unicorns have GCCs in India (notable names being Uber, Grab, Gojek). However, this segment will be one of the biggest growth drivers.
Currently, only 10% of the GCCs in India are from Asia Pacific organisations. Some of the prominent names being Hitachi, Rakuten, Panasonic, Samsung, LG, and Foxconn. Asian MNCs have an opportunity to move fast and stay relevant. This segment is also expected to grow disproportionately.
New age GCCs in India have the potential to be the crown jewel for global MNCs. For India, this has a huge potential for job creation and development of Smart City ecosystems. In this decade, growth of GCCs will be one of the core pillars of India’s journey to a USD 5 trillion economy.
The views and opinions mentioned in the article are personal.
Anupam Verma is part of the Senior Leadership team at ICICI Bank and his responsibilities have included leading the Bank’s strategy in South East Asia to play a significant role in capturing Investment, NRI remittance, and trade flows between SEA and India.

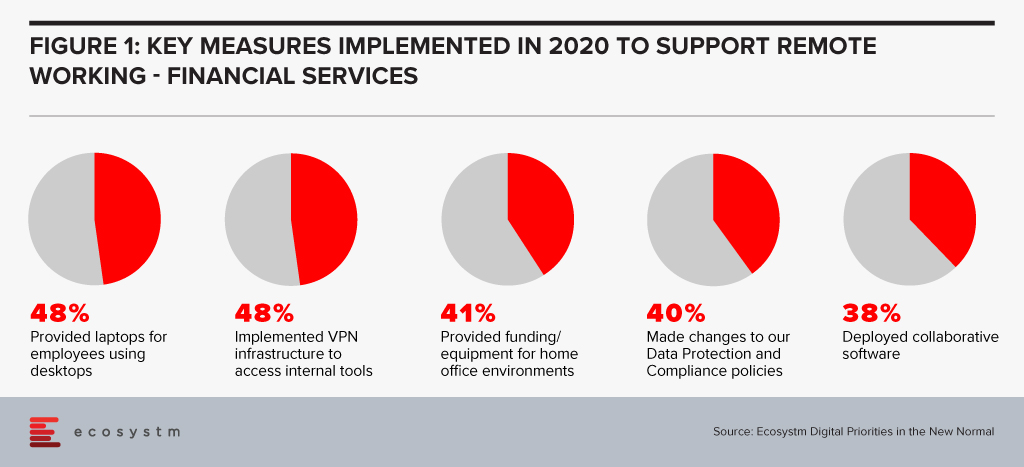
Financial services institutions made a fast switch to remote working when the pandemic forced widespread lockdowns across the globe. The adoption of remote working was nascent in the industry, and there was a need for a fast pivot by both the organisations and employees (Figure 1).
However, this has also exposed the industry to technology-related risks. Ecosystm Principal Advisor, Gerald Mackenzie says, “The move to a more virtualised working environment has been a trend taking shape for many years and like so many trends, it needed an impetus to make it a norm; in this case COVID-19.”
“Many, if not most, financial institutions have been shifting to more cloud-based and modularised Banking-as-a-Service (BaaS) models and these trends will only accelerate as we need to manage risks inherent in conducting financial services via remote working environments. For example, critical capabilities such as Advisor to Client communications need to be verifiable and auditable whether they are happening inside or outside of the office and I predict regulators will be pushing financial institutions to ensure these standards become the norm rather than the exception.”
Singapore Addresses Risk in the Financial Industry
To manage and mitigate risks that could emerge from the extensive remote working adoptions by FIs, The Monetary Authority of Singapore (MAS) and The Association of Banks in Singapore (ABS) jointly released a paper titled Risk Management and Operational Resilience in a Remote Working Environment. This is also in line with the previous collaboration between MAS and ABS in May 2020 to establish the Return to Onsite Operations Taskforce (ROOT). ROOT sought to strengthen and implement safe management and operational resilience measures as well as endorsement of industry best practices.
The paper seeks to create awareness amongst financial institutions on key remote working risks in the domains of technology, operations, security, fraud, staff misconduct, legal and regulatory risks. MAS encourages them to take pre-emptive measures to adopt good practices on managing risks.
Mackenzie adds, “Of course, some of the issues are difficult to solve. For example, staff accessing client data from their homes creates inherent vulnerabilities and the ways to ensure staff have suitable ‘in-home’ working environments to effectively manage these risks can be challenging and expensive. There are great opportunities for innovators to adapt solutions to solve these problems in what will undoubtedly be a growing investment area for many Financial Institutions.” The paper also examines various controls on the people and culture leveraging examples drawn from the experiences of ABS member banks to address evolving risks. For instance, FIs can implement security controls on staff infrastructure including their personal devices, verify in-person meetings against original documents, timely response strategies for recovery teams, legal risks and more.
To keep pace with the changing trends in technology deployment, risk management, and cybersecurity, MAS has been regularly working and engaging with experts to introduce guidelines, principles and best practices for financial institutions. In February, MAS issued a consultation paper proposing revisions to enhance the current requirements for enterprise risk management, investment risk management and public disclosure practices for insurers. Similarly, in January, MAS issued risk management best practice and standards to guide financial institutions in managing technology risk and maintain IT and cyber resilience.
Get insights on the technology areas in the Financial services industry that will see continued investments, as organisations get into the recovery phase.

Environmental, social, and governance (ESG) ratings towards investment criteria have become popular for potential investors to evaluate companies in which they might want to invest. As younger investors and others have shown an interest in investing based on their personal values, brokerage firms and mutual fund companies have begun to offer exchange-traded funds (ETFs) and other financial products that follow specifically stated ESG criteria. Passive investing with robo-advisors such as Betterment and Wealthfront have also used ESG criteria to appeal to this group.
The disruption caused by the pandemic has highlighted for many of us the importance of building sustainable and resilient business models based on multi-stakeholder considerations. It has also created growing investor interest in ESG.
ESG signalling for institutional investors
The increased interest in climate change, sustainable business investments and ESG metrics is partly a reaction of the society to assist in the global transition to a greener and more humane economy in the post-COVID era. Efforts for ESG standards for risk measurement will benefit and support that effort.
A recent study of asset managers by the investment arm of Institutional Shareholder Services (ISS) showed that more than 12% of respondents reported heightened importance of ESG considerations in their investment decisions or stewardship activities compared to before the pandemic.
In the area of hedge funds, there has been an increased demand for ESG-integrated investments since the start of COVID-19, according to 50% of all respondents of a hedge fund survey conducted by BNP Paribas Corporate and Institutional Banking of 53 firms with combined assets under management (AUM) of at least USD 500B.
ESG criteria may have a practical purpose beyond any ethical concerns, as these criteria may be able to help avoidance of companies whose practices could signal risk. As ESG gets more traction, investment firms such as JPMorgan Chase, Wells Fargo, and Goldman Sachs have published annual reports that highlight and review their ESG approaches and the bottom-line results.
But even with more options, the need for clarity and standards on ESG has never been so important. In my opinion, there must be an enhanced effort to standardise and harmonise ESG rating metrics.
How are ESG ratings made?
ESG ratings need both quantitative and qualitative/narrative disclosures by companies in order to be calculated. And if no data is disclosed or available, companies then move to estimations.
No global standard has been defined for what is included in a given company’s ESG rating. Attempts at standardising the list of ESG topics to consider include the materiality map developed by the Sustainable Accounting Standard Board (SASB) or the reporting standards created by the Global Reporting Initiative (GRI). But most ESG rating providers have been defining their own materiality matrices to calculate their scores.
Can ESG scoring be automatically integrated?
Just this month, Morningstar equity research analysts announced they will employ a globally consistent framework to capture ESG risk across over 1,500 stocks. Analysts will identify valuation-relevant risks for each company using Sustainalytics’ ESG Risk Ratings, which measure a company’s exposure to material ESG risks, then evaluate the probability those risks materialise and the associated valuation impact. ESG rating firms such as MSCI, Sustainalytics, RepRisk, and ISS use a rules-based methodology to identify industry leaders and laggards according to their exposure to ESG risks, as well as how well they manage those risks relative to peers.
Their ESG Risk Ratings measure a company’s exposure to industry-specific material ESG risks and how well a company is managing those risks. This approach to measuring ESG risk combines the concepts of management and exposure to arrive at an assessment of ESG risk – the ESG Risk Rating – which should be comparable across all industries. But some critics of this form of approach feel it is still too subjective and too industry-specific to be relevant. This criticism is relevant when you understand that the use of the ESG ratings and underlying scores may in future inform asset allocation. How might this better automated and controlled? Perhaps adding some AI might be useful to address this?
In one example, Deutsche Börse has recently led a USD 15 million funding round in Clarity AI, a Spanish FinTech firm that uses machine learning and big data to help investors understand the societal impact of their investment portfolios. Clarity AI’s proprietary tech platform performs sustainability assessments covering more than 30,000 companies,198 countries,187 local governments and over 200,000 funds. Where companies like Cooler Future are working on an impact investment app for everyday individual users, Clarity AI has attracted a client network representing over $3 trillion of assets and funding from investors such as Kibo Ventures, Founders Fund, Seaya Ventures and Matthew Freud.
What about ESG Indices? What do they tell us about risk?
Core ESG indexing is the use of indices designed to apply ESG screening and ESG scores to recognised indices such as the S&P 500®, S&P/ASX 200, or S&P/TSX Composite. SAM, part of S&P Global, annually conducts a Corporate Sustainability Assessment, an ESG analysis of over 7,300 companies. Core ESG indices can then become actionable components of asset allocation when a fund or separately managed accounts (SMAs) provider tracks the index.
Back in 2017, the Swiss Federal Office for the Environment (FOEN) and the State Secretariat for International Finance (SIF) made it possible for all Swiss pension funds and insurance firms to measure the environmental impact of their stocks and portfolios for free. Currently, these federal bodies are testing use case with banks and asset managers. Its initial activities will be recorded in an action plan, which is due to be published in Spring 2021.
How can having a body of sustainable firms help create ESG metrics?
Creating ESG standard metrics and methodologies will be aided when there is a network of sustainable companies to analyse, which leads us to green fintech networks (GFN) of companies interested in exploring how their own technology investments can be supportive of ESG objectives. Switzerland is setting up a Green Fintech Network to help the country take advantage of the “great opportunity” presented by sustainable finance. The network has been launched by SIF alongside industry players, including green FinTech companies, universities, and consulting and law firms. Stockholm also has a Green Fintech Network that allows collaboration towards sustainability goals.
Concluding Thought
We should be curious about how ESG can provide decision-oriented information about intangible assets and non-financial risks and opportunities. More information and data from ESG data providers like SAM, combined with automation or AI tools can potentially provide a more complete picture of how to measure the long-term sustainable performance of equity and fixed income asset classes.
Singapore FinTech Festival 2020: Investor Summit
For more insights, attend the Singapore FinTech Festival 2020: Investor Summit which will cover topics tied to 2021 Investor Priorities, and Fundraising and exit strategies

CEOs have an active role to play in an organisation’s transformation needs and journey – including in the technology decisions. Last month we spoke about why CEOs should get involved in their organisation’s IoT investments. Now, we look at Cloud – which has been a part of the CIO’s purview so far. Under the current circumstances, most organisations are actively pushing to go digital and the internal discussions will often revolve around empowering remote employees and digital customers. All the technologies that are being evaluated by organisations today have Cloud as their pillar. Increasingly, we see organisations adopt the hybrid and the multi-cloud. And organisations may not have the capabilities – technological and skills – to support the complexity of their Cloud environment. While a CEO does not have to understand the technology fully, it is important to understand the business impact of the technology.
Why should a CEO get involved in and have visibility into an organisation’s Cloud investments? There are a few important reasons.
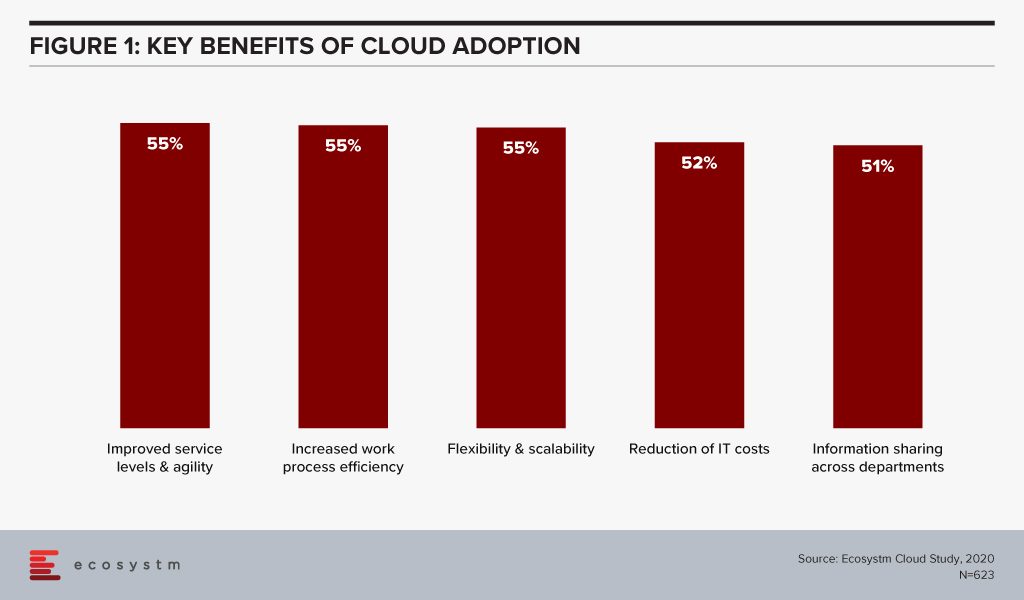
#1 Cloud is not a cost-saving measure – it will enable you to transform
Organisations have matured in their Cloud adoption and no longer evaluate the benefits of Cloud only in terms of shifting CapEx to OpEx. If we look at the benefits of Cloud adoption, reduction of IT costs is not even in the top 3 benefits that organisations are seeking from Cloud anymore. Operational efficiency and collaboration emerge as key benefits (Figure 1) – while some companies still move to the Cloud for the savings, they stay there for other benefits.
This requires organisations to think of Cloud as a technology empowering their infrastructure and services. Cloud acts as an enabler for ease of doing business, real-time data access for productivity increase, and process automation. This impacts the entire organisation. It also involves prioritising the needs of certain functions over others – definitely not what a CIO should have to do.
If we look at just Cloud storage as an example, organisations can no longer have individual functions and their associated shadow IT teams having their own Cloud storage (and collaboration). This often turns out to be more expensive and there is a lack of consolidated view and management. While organisations forge ahead with the dream of having real-time information sharing across functions, a CIO has to consider the entire organisation’s technological and business needs – a CEO is the best person to guide the CIO in translating the organisation’s vision into IT priorities.
#2 In fact Cloud adoption may not cut costs at all!
Organisations are also re-evaluating the cost benefits of Cloud. Investing in a Cloud infrastructure with a short-term view on the investments involved has led to instances of Cloud solutions being brought back in-house because of rising costs. While security, data privacy and integration remain the key challenges of Cloud adoption (Figure 2), over a third of the organisations find Cloud more expensive than traditional licensing or owning the hardware.
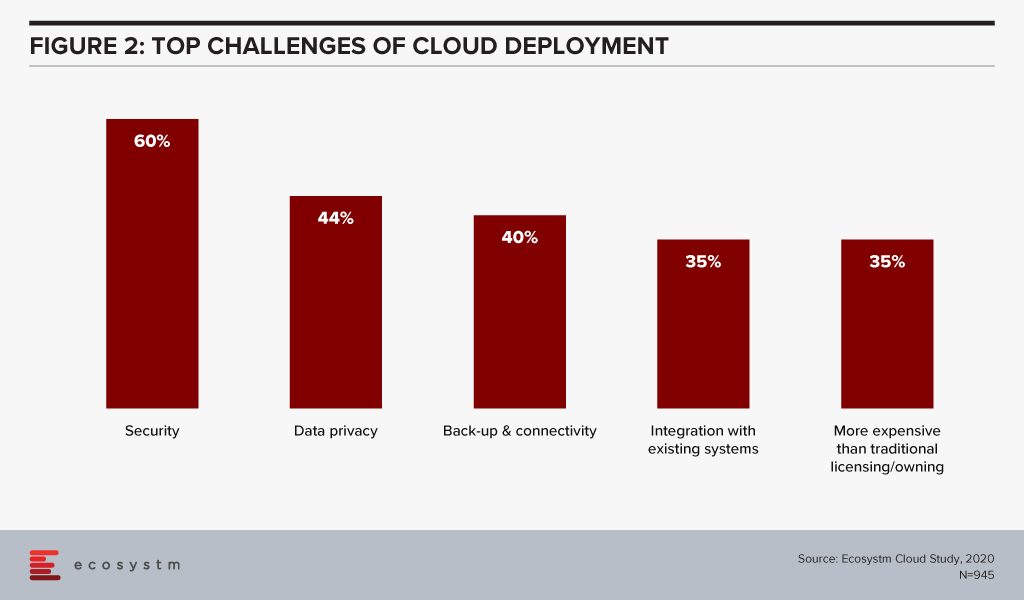
Organisations find that the cost considerations do not stop after the adoption or migration. As businesses use Cloud to scale, there are several aspects that require constant re-evaluation and often further investments – cybersecurity measures, continuous data protection (CDP), disaster recovery management, rightsizing capacity, software and database licenses and day-to-day maintenance, to name a few. In addition to this, the cost of finding and recruiting a team of professionals to manage and maintain the Cloud environment also adds up to the OpEx.
If the CIO is talking about a Cloud migration for cost benefits only, the CEO and the CFO need to step in to evaluate that all factors have been taken into consideration. Moreover, the CIO may not have full visibility of how and where the organisation is looking to scale up or down. It is the CEO’s responsibility to share that vision with the CIO to guide Cloud investments.
#3 Cloud will increasingly be part of all tech adoption considerations
In this disruptive world, CEOs should explore possibilities and understand the technical capabilities which can give organisations an edge over their competitors. It is then up to the CIOs to implement that vision with this larger context in mind. As organisations look to leverage emerging technologies, organisations will adopt Cloud to optimise their resources and workloads.
AI is changing the way organisations need to store, process and analyse the data to derive useful insights and decision-making practices. This is pushing the adoption of Cloud, even in the most conservative organisations. Cloud is no longer only required for infrastructure and back-up – but actually improving business processes, by enabling real-time data and systems access. Similarly, IoT devices will grow exponentially. Today, data is already going into the Cloud and data centres on a real-time basis from sensors and automated devices. However, as these devices become bi-directional, decisions will need to be made in real-time as well. Edge Computing will be essential in this intelligent and automated world. Cloud platform vendors are building on their edge solutions and tech buyers are increasingly getting interested in the Edge allowing better decision-making through machine learning and AI.
In view of the recent global crisis, we will see a sharp uptake of Cloud solutions across tech areas. IaaS will remain the key area of focus in the near future, especially Desktop-as-as-Service. Organisations will also look to evaluate more SaaS solutions, in order to empower a mobile and remote workforce. This will allow the workforce of the future to stay connected, informed and make more decisions. More than ever, CEOs have to drive business growth with innovative products and services – not understanding the capabilities and challenges of Cloud adoption and the advancements in the technology can be a serious handicap for CEOs.
#4 Your IT Team may be more complacent about Cloud security than you think
Another domain that requires the CEO’s attention is cybersecurity. The Cloud is used for computing operations and to store data including, intellectual property rights, financial information, employee details and other sensitive data. Cybersecurity breaches have immense financial and reputational implications and IT Teams cannot solely be responsible for it. Cybersecurity has become a Board-level conversation and many organisations are employing a Chief Information Security Officer (CISO) who reports directly into the CEO. Cybersecurity is an aspect of an organisation’s risk management program.
Evaluating the security features of the Cloud offerings, therefore, becomes an important aspect of an IT decision-maker’s job. While security remains a key concern when it comes to Cloud adoption, Cloud is often regarded as a more secure option than on-premise. Cloud providers have dedicated security focus, constantly upgrade their security capabilities in response to newer threats and evolve their partner ecosystem. There is also better traceability with the Cloud as every virtual activity can be tracked, monitored, and logged. Ecosystm research finds that more than 40% of IT decision-makers think the Public Cloud has enough security measures and does not need complementing (Figure 3).
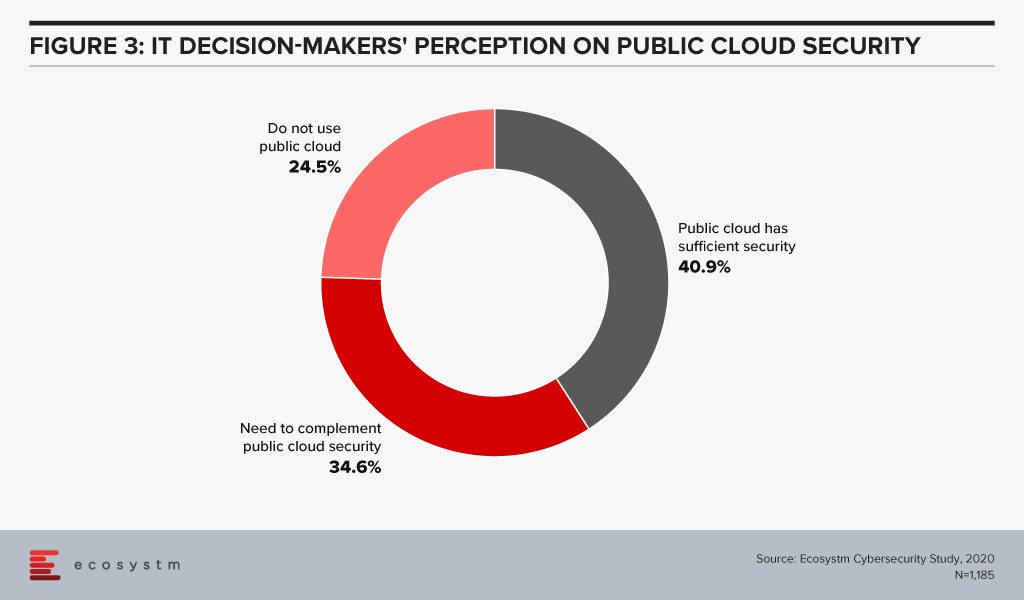
However, the Cloud is as secure as an organisation makes it. The perception that there is no need to supplement Public Cloud security features can have disastrous outcomes. It is important to supplement the Cloud provider’s security with event-driven security measures within an organisation’s applications and cloud interface.
It is the job of the CEO – through the CISO – to evaluate how cyber ready the IT Team really is. Do they know enough about shared responsibility? Do they have full cognizance of the SLAs of their Cloud providers? Do they have sufficient internal cybersecurity skills? Do they understand that data breaches can have cost and reputational impacts? As cybersecurity breaches begin to have more financial implications than ever and can derail an organisation, a CEO should have visibility of the risks of the organisation’s Cloud adoption.
Cloud is no longer just a technological decision – it is a business decision and takes into account the organisation’s vision. A full visibility of the Cloud roadmap – including the pitfalls, the risks and the immense potential – will empower a CEO immensely.

A report published by PWC last year states that “While CIOs and CISOs can take care of the technological aspects and in some cases compliance, the business risk, which is now apparent after the emergence of endless breaches in large conglomerates, can best be understood and managed in the boardroom.”
While I agree that cybersecurity is both an operational and business risk, the question of understanding the threat landscape and the risk exposure/risk position of the company falls on both parts of the business. The Board is responsible for the exposure and financial remediation of cyber risk, whereas the IT management is more operationally responsible for prioritisation of actions and remedies. But they need to be able to communicate on this topic together from both sides of the equation. Ecosystm research finds that 98% of global organisations involve the Board to drive their cybersecurity vision, while 88% of organisations look to their IT teams for operational management.
So, where do these two parties meet? How does the risk position of the company get communicated to both parties in such a way that they can both take the necessary actions and prioritise the resource allocation?
Dashboards for Discussion
This is where the discussion on cyber risk dashboards comes up. It is not a new topic, but some of the more recent solutions introduced in the market move beyond penetration testing to really highlighting the risk posture of the business and where resources should be allocated, as well as where the business compares to others in their industry. I will give a specific example of one such approach a bit later in this blog post.
I find the gamification aspect (e.g. industry comparison) a real driver for the Boardroom, as it allows them to position their risk profile against others to the relevant stakeholders and regulators of the business. Actionable metrics that can also be compared to others gives a feeling of control over a situation that frequently lacks control boundaries.
Maturity models vs. risk profiles
In the PwC article I mentioned earlier [written last year by Sivarama Krishnan], the focus was on actions the Board can take, which include the usual discussions of cyber insurance, data handling policies, reporting structures and a tie into the strategy of the business overall. But at a top-level, setting these kinds of priorities can only work when you have some form of metric checking to assess how operationally these kinds of strategic decisions are working for the business.
Figure 1: Barometric Reporting Scale
Source: PwC, March 2019
Having a reporting scale that is not only relevant and measurable but also actionable is key to tying the strategic decisions to the operational activities and overall resource and time allocations. You could use a cyber risk strategy framework, such as this one shown in Figure 1, but it needs to be fed with real-time information on the risk position of the business.
Creating actionable metrics
I mentioned previously that there is a need for solutions that create a communication point between the Board and the operational IT teams as to what risk position exists for the business, and how they compare to others in their industry.
Dashboards that create an overview of the risk portfolio exist, but they do not always tie to specific financial impacts to the business. Integrated risk management platforms, such as the one from CyberSaint Security, prioritise cybersecurity as a business risk and give access to the Board to have the ability to drill down into their compliance and risk posture across business units, asset types, projects and regions.
But one of the more concerning aspects of cybersecurity recently is ransomware, which locks up operations until a ransom is paid. One such solution that focuses specifically on the financial impact on the bottom line of ransomware comes from RiskSense and was launched last month. As a background, the RiskSense Platform utilises machine learning, risk-based scoring and analytics combined with technology-accelerated penetration testing, and then identifies and prioritises remediation of critical vulnerabilities that place organisations at risk.
Given the concern at the Board level on Ransomware, RiskSense decided to focus on the very vulnerabilities that make ransomware attacks possible. They recently announced their RiskSense Ransomware Dashboard which reveals all assets within the IT structure that are at risk to active exploits used by ransomware in the wild. This Dashboard examines the vulnerabilities used by ransomware based on risk factors including the presence of dangerous remote code execution (RCE) and privilege escalation (PE) capabilities, as well as vulnerabilities that are “trending” to narrow and identify which should be prioritised for immediate remediation.
Figure 2: RiskSense Executive Dashboard
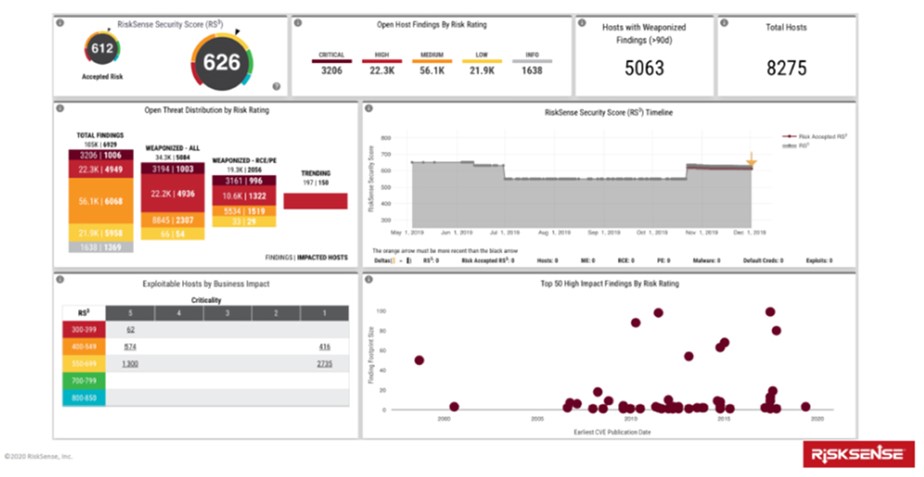
Source: RiskSense, January 2020
In my opinion, this specific example highlights the two unique features of the RiskSense Ransomware Dashboard. For IT management, it is its ability to contextualise the threat landscape to highlight priorities and position the current security posture of the company. And for the Board, it is to compare the situation of the company to others in their industry to benchmark within the industry domain how effectively their cybersecurity efforts have been deployed. It puts the security team in more of an offensive (vs. defensive) mode towards its cybersecurity efforts and outcomes. And it allows the IT team to be able to communicate the risk position of the business to the Board with a series of actionable steps to address the vulnerability.
So from a communications aspect, and that of a shared resource to view vulnerabilities and actions, the introduction of the RiskSense Ransomware Dashboard makes financial risk sense, if you will pardon the pun.
Risk transparency
For both regulatory and financial reasons, Board-level executives need to have cyber risk information for business decisions. This means having access to drill-down capabilities that show gap analyses from the category to the control level for various frameworks or standards. This might include either the NIST Cybersecurity Framework, CIS Critical Security Controls, ISO27002 or various privacy standards such as the NIST Privacy Framework and emerging California Consumer Privacy Act (CCPA).
Dashboards that tie to these frameworks do exist, but they need to be able to be used for communication of actionable activities and resource allocation, not just as a reporting mechanism for regulatory bodies and shareholders. The RiskSense Ransomware Dashboard discussed above is one good example of making transparency actionable and comparable. We need more of those in the industry to keep the communication flowing.